IEEE 802.1X
 Generated by GPT-5-mini
Generated by GPT-5-miniExpansion Funnel Raw 82 → Dedup 0 → NER 0 → Enqueued 0
| IEEE 802.1X | |
|---|---|
 | |
| Name | IEEE 802.1X |
| Status | Published standard |
| Developed by | Institute of Electrical and Electronics Engineers |
| First published | 2001 |
| Domain | Network access control, authentication |
IEEE 802.1X IEEE 802.1X is a network access control protocol for port-based authentication used to secure wired and wireless Cisco switched Ethernet, Juniper deployments, and enterprise Aruba WLANs. It provides an authentication framework between a client, an authenticator, and an authentication server in environments managed by organizations such as IETF-aligned operators and research institutions like MIT and Stanford University. 802.1X underpins secure access in products from HP, Dell, IBM and interoperates with directory services including Active Directory and OpenLDAP.
Overview
802.1X defines a mechanism where an endpoint called a supplicant requests access through an authenticator (typically a switch or wireless access point) which relays credentials to an authentication server such as FreeRADIUS or Network Policy Server. Major implementations reference work from PARC research and standards committees at ITU and ISO for layered networking. Widely deployed across enterprise campuses like those of Google and Facebook, it supports centralized policy enforcement in data centers operated by AWS and Azure and integrates with identity providers such as Okta and Ping.
Architecture and Components
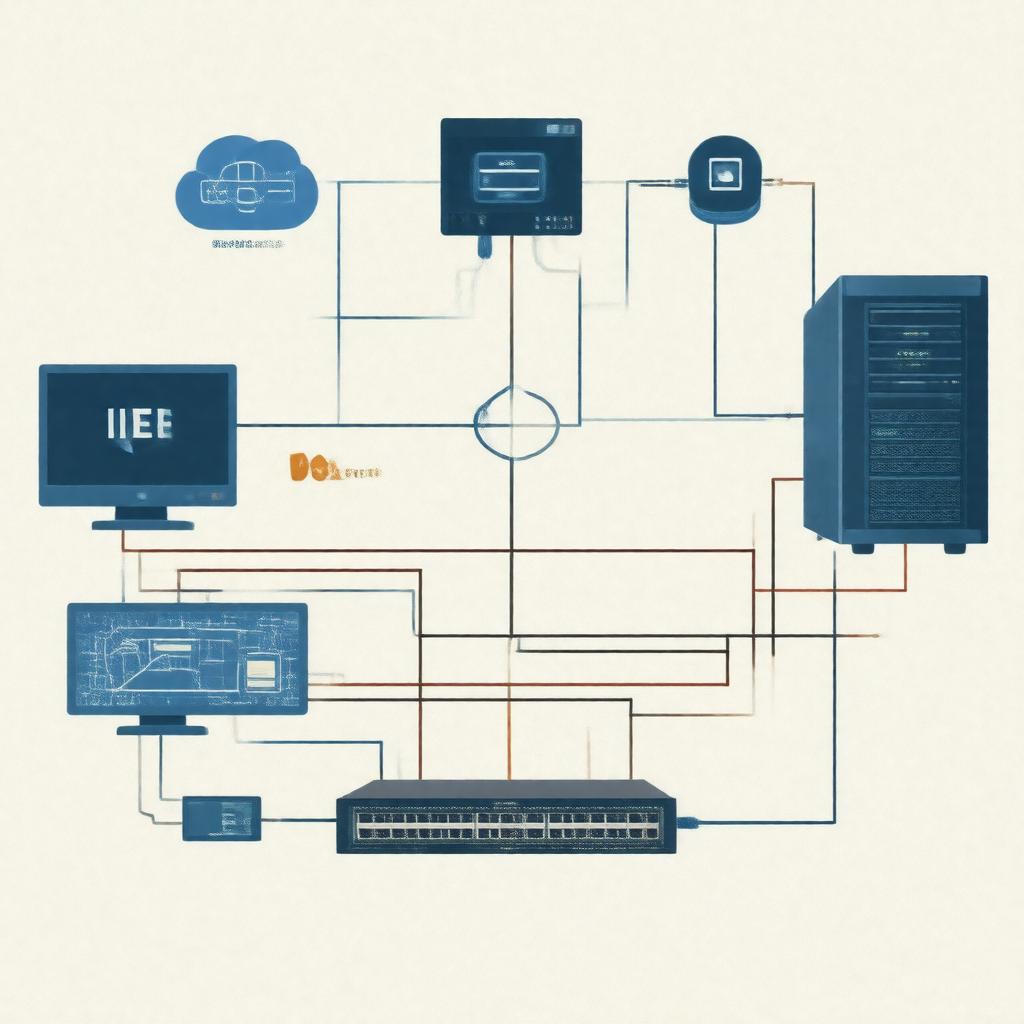
The 802.1X architecture comprises three logical entities: supplicant (client), authenticator (switch or access point), and authentication server (RADIUS/AAA). Supplicants are often devices running operating systems from Windows, macOS/iOS, Linux distributions, or mobile platforms like Android. Authenticators include equipment from Cisco, Aruba, Ruckus, and Netgear, while authentication servers commonly implement RADIUS protocols defined by the IETF and use back-end stores such as Active Directory or LDAP. The protocol leverages Extensible Authentication Protocol ports and ports control mechanisms standardized within IEEE 802 family work and aligns with link-layer control standards like Ethernet and Wi‑Fi.
Authentication Protocols and EAP Methods
802.1X carries EAP (Extensible Authentication Protocol) over LANs, supporting methods including EAP-TLS, EAP-TTLS, PEAP, EAP-FAST, and EAP-MSCHAPv2, which are specified or referenced by organizations such as IETF, ISOC, and contributors from Cisco and Microsoft. EAP-TLS relies on certificate infrastructures often issued by certificate authorities like DigiCert or Let's Encrypt and integrated with PKI operated by entities such as Entrust. PEAP and EAP-MSCHAPv2 are commonly used in mixed environments managed by enterprises including Bank of America and Walmart for legacy client compatibility. Advanced methods and extensions are discussed in IETF documents and adopted in deployments by cloud providers such as GCP and IBM Cloud.
Deployment and Use Cases
Common 802.1X use cases include securing enterprise wired ports in corporate campuses operated by Siemens, guest and employee wireless access in hospital networks like those at Mayo Clinic and academic campuses such as UC Berkeley, and NAC enforcement in carrier networks run by Verizon and AT&T. Data center deployments incorporate 802.1X for device authentication in environments managed by Oracle and VMware. Telecommunications operators including NTT and Deutsche Telekom apply 802.1X in managed services, while managed service providers like Accenture and Capgemini use it for client segmentation and compliance with standards such as regulations overseen by FCC and audit regimes by ISACA.
Security Considerations and Vulnerabilities
While 802.1X improves perimeter control, implementations can be vulnerable to attacks like MAC spoofing, rogue access points, and EAP downgrade exploits documented by researchers at CERT and academic groups from CMU and ETH Zurich. Misconfigured RADIUS servers and weak EAP methods (for example, poorly protected MSCHAPv2) have been implicated in breaches affecting organizations including Target and Sony Pictures. Mitigations include certificate-based EAP-TLS deployment using PKI from authorities such as Entrust or DigiCert, network segmentation concepts from Cisco and enforcement via network access control appliances from Forescout and Palo Alto. Standards bodies like IEEE SA and security communities such as OWASP recommend defense-in-depth, continuous monitoring with tools from Splunk and incident response coordination with agencies like CISA.
Interoperability and Standards Evolution
Interoperability testing has been conducted by consortia and industry groups including Wi-Fi Alliance and ONF, with multi-vendor interoperability events featuring vendors such as Cisco, Aruba, Extreme Networks, and HPE. The 802.1 working group within IEEE SA has evolved the standard alongside related projects like MACsec and WPA2/WPA3 efforts, and coordination with IETF for RADIUS extensions and EAP improvements. Ongoing development considers integration with modern identity frameworks from SAML-using providers and OAuth 2.0 ecosystems championed by companies including Auth0 and Okta, and with zero trust architectures promoted by NIST and industry leaders such as Google (BeyondCorp).
Category:Computer networking standards