ICMP
 Generated by GPT-5-mini
Generated by GPT-5-miniExpansion Funnel Raw 85 → Dedup 12 → NER 7 → Enqueued 1
| ICMP | |
|---|---|
 | |
| Name | ICMP |
| Full name | Internet Control Message Protocol |
| Introduced | 1981 |
| Defined in | RFC 792 |
| Layer | Internet Layer |
| Status | Active |
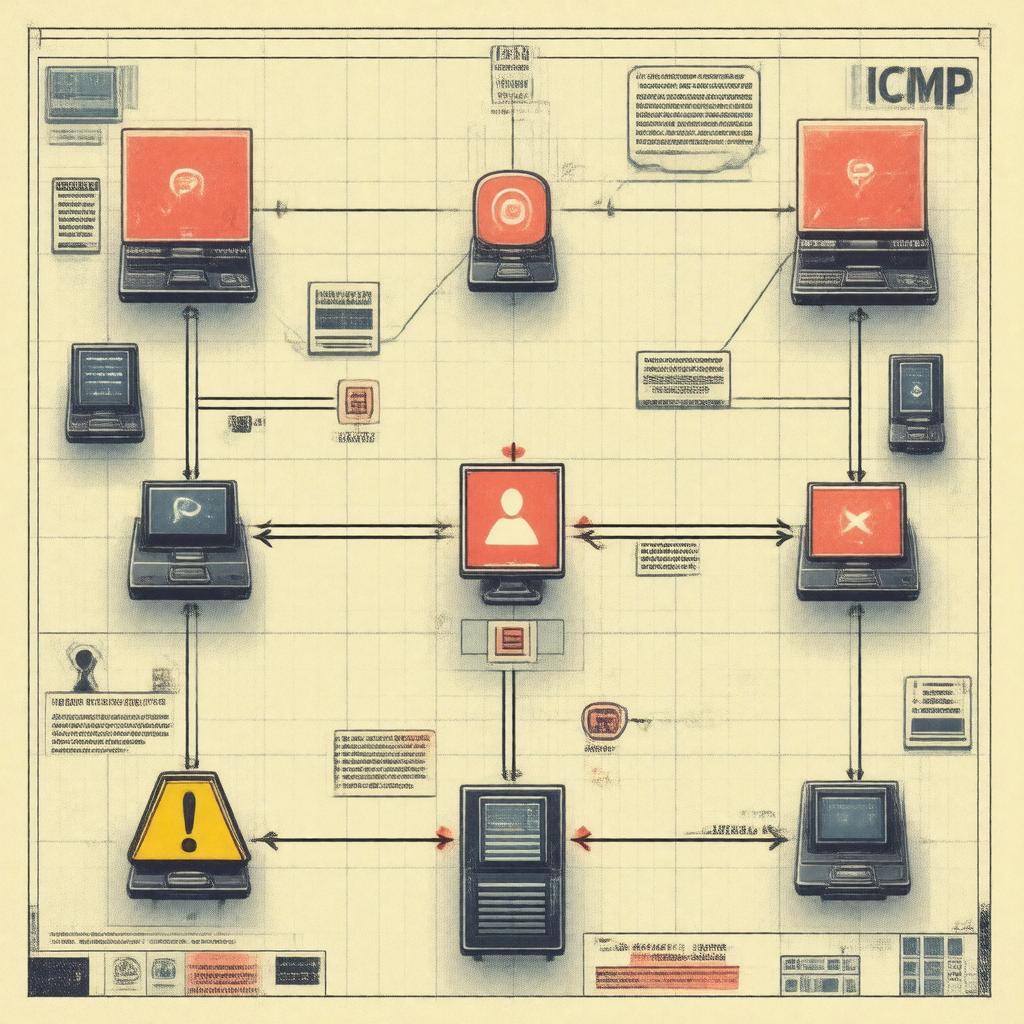
ICMP ICMP is a network-layer control protocol used for reporting errors, diagnostics, and operational information within Internet Protocol networks. Designed as part of the ARPANET/Internet Protocol Suite development, ICMP conveys control messages between hosts, routers, and gateways to support packet delivery and network management. Implementations of ICMP appear across operating systems, routers, firewalls, and network stacks maintained by vendors and standards bodies.
Overview
ICMP functions alongside IPv4 and IPv6 to signal issues like unreachable destinations, time exceeded, and echo requests and replies. It is specified in foundational documents such as RFC 792 and later extensions; implementations interact with projects and organizations including the Internet Engineering Task Force, Internet Assigned Numbers Authority, Cisco Systems, Juniper Networks, and Linux Foundation. ICMP messages are encapsulated in IP datagram payloads and are processed by network devices like routers, switches, firewall appliances, and host TCP/IP stacks in systems produced by corporations such as Microsoft Corporation, Apple Inc., IBM, and Oracle Corporation.
Protocol Details
ICMP uses an 8-bit protocol number in the IP header of IPv4; in IPv6 a related protocol, ICMPv6, uses a distinct header and expanded functionality. The protocol defines a Type field, a Code field, and a checksum; payloads often include portions of the triggering IP packet to aid diagnosis. Standards and updates are discussed in IETF working groups and documented in RFC series, with influence from institutions like MIT, Stanford University, University College London, and companies such as Hewlett-Packard and Intel Corporation. Implementations integrate with networking stacks in projects like FreeBSD, OpenBSD, NetBSD, Android (operating system), and Windows NT.
Message Types and Codes
ICMP classifies messages into types with subordinate codes; common examples include Echo Request/Reply for diagnostics, Destination Unreachable with codes for fragmentation needed or protocol unreachable, and Time Exceeded for TTL expiry. Specific types are referenced in standards bodies and implemented by vendors including Cisco Systems, Huawei Technologies, Arista Networks, and MikroTik. Diagnostic messages support utilities developed by authors and projects such as Van Jacobson-related tools, network utilities from GNU Project, and vendor toolsets used by AT&T, Verizon, and Deutsche Telekom.
Implementation and Operation
ICMP is implemented in kernel network stacks in systems by Microsoft Corporation, Apple Inc., Google LLC, Red Hat, and community projects like Debian and Ubuntu. Routers from Cisco Systems, Juniper Networks, and Huawei Technologies generate ICMP for forwarding failures; load balancers from F5 Networks and Citrix Systems may interact with ICMP for health checks. Network operators at organizations such as Cloudflare, Akamai Technologies, Amazon Web Services, and Google Cloud Platform tune ICMP handling for performance and security. Development and testing involve tools and suites from Wireshark Foundation, Iperf, Netcat, and Nmap.
Security and Vulnerabilities
ICMP has been exploited for reconnaissance and denial-of-service attacks; historical incidents involved misuse in amplification and flood attacks affecting infrastructures run by America Online, Verizon Communications, and Sprint Corporation. Vulnerabilities prompted mitigation guidance from CERT Coordination Center, US-CERT, and vendors like Cisco Systems and Microsoft Corporation. Network defense techniques are employed by security firms such as Palo Alto Networks, Fortinet, CrowdStrike, and Symantec to filter or rate-limit ICMP while balancing diagnostic needs. Research on ICMP misuse has been published by academic groups at MIT CSAIL, Carnegie Mellon University, University of California, Berkeley, and Georgia Institute of Technology.
Usage and Diagnostics
Common diagnostic utilities using ICMP include ping, traceroute (ICMP and UDP/TCP variants), and path MTU discovery implementations used in operating systems by Microsoft Corporation, Apple Inc., Linux Foundation distributions, and network tool authors like Van Jacobson. Network management platforms from SolarWinds, Nagios, Zabbix, and PRTG Network Monitor incorporate ICMP probes to assess reachability. Content delivery networks like Cloudflare and Akamai Technologies monitor ICMP behavior to manage routing, while ISPs such as Comcast, BT Group, and NTT Communications use ICMP-derived metrics in traffic engineering.
History and Standards
ICMP was first standardized in RFC 792 (1981) during early ARPANET to Internet Protocol development, with subsequent enhancements appearing in documents in the RFC series and IETF drafts. Key contributors and institutions include researchers affiliated with BBN Technologies, DARPA, University of California, Los Angeles, and standards participants from IBM and Xerox PARC. Later work produced ICMPv6 defined in RFC 4443 and related IPv6 specifications influenced by projects at RIPE NCC and IANA. Adoption and evolution have been driven by vendors like Cisco Systems, Juniper Networks, and open-source communities such as The FreeBSD Project and The Linux Kernel Organization.
Category:Internet protocols