TCP/IP protocol suite
 Generated by DeepSeek V3.2
Generated by DeepSeek V3.2Expansion Funnel Raw 59 → Dedup 8 → NER 4 → Enqueued 1
| TCP/IP protocol suite | |
|---|---|
 | |
| Name | TCP/IP protocol suite |
| Developer | DARPA, Vint Cerf, Bob Kahn |
| Introduced | 0 1982 |
| Based on | ARPANET |
| Influenced | Internet, World Wide Web |
TCP/IP protocol suite. The Transmission Control Protocol/Internet Protocol suite is the foundational set of communication protocols that enables data exchange across interconnected networks, forming the global Internet. Its development, spearheaded by American computer scientists Vint Cerf and Bob Kahn under the auspices of the Defense Advanced Research Projects Agency (DARPA), provided a robust, packet-switched framework that succeeded earlier network models like the ARPANET. The suite's standardized, open architecture, formalized in documents known as Request for Comments (RFCs) published by the Internet Engineering Task Force (IETF), ensures interoperability between diverse hardware and software systems from vendors like Cisco Systems and Microsoft.
Overview
The TCP/IP protocol suite defines the rules and conventions for digital communication, allowing devices from different manufacturers and running different operating systems, such as Unix or Windows NT, to communicate seamlessly. It operates on the principle of packet switching, where data is broken into discrete blocks that are routed independently across a network, a concept distinct from the circuit-switched methodology of the traditional Public Switched Telephone Network. This design is inherently decentralized and fault-tolerant, enabling the network to survive partial outages, a key requirement of its early military sponsors during the Cold War. The suite's protocols are implemented in everything from supercomputers at CERN to smartphones using Android.
Core protocols
The suite is named for two of its most essential protocols. The Transmission Control Protocol (TCP) provides reliable, connection-oriented data delivery, ensuring packets arrive in order and without errors, which is critical for applications like web browsing and email. Its counterpart, the Internet Protocol (IP), is responsible for the fundamental tasks of addressing and routing packets across networks; the widely deployed IPv4 uses 32-bit addresses, while its successor, IPv6, greatly expands the address space. Other vital protocols include the User Datagram Protocol (UDP) for connectionless, low-latency communication used in Voice over IP and Domain Name System (DNS) queries, and the Internet Control Message Protocol (ICMP) used for diagnostic functions by utilities like ping.
Architecture and layers
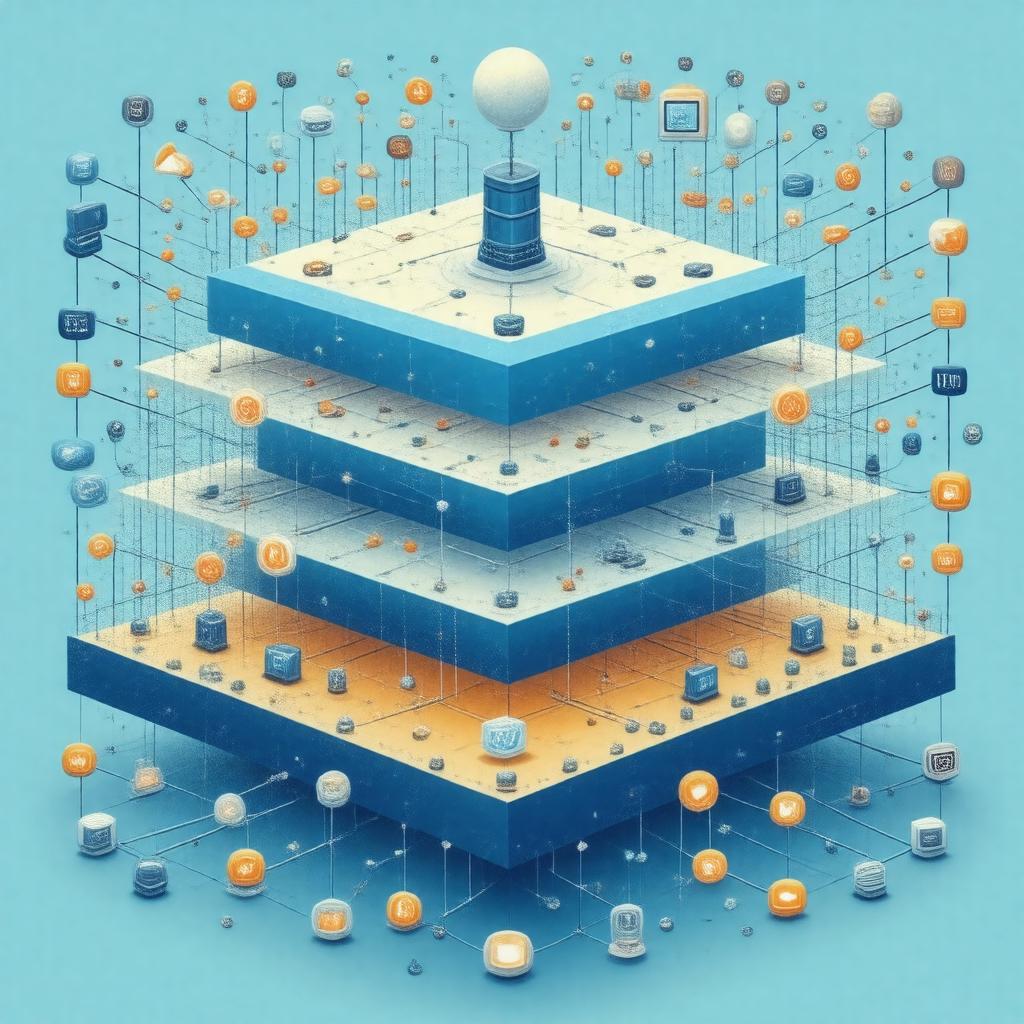
The TCP/IP model organizes its functions into four abstraction layers, a simplification of the seven-layer OSI model developed by the International Organization for Standardization. The lowest **Link layer** (e.g., Ethernet, Wi-Fi) handles communication on the physical network segment. The **Internet layer**, primarily using IP, routes packets between different networks, potentially traversing routers from companies like Juniper Networks. The **Transport layer**, with TCP and UDP, manages end-to-end communication between host applications. The top **Application layer** encompasses protocols for specific user services, such as Hypertext Transfer Protocol (HTTP) for the World Wide Web, Simple Mail Transfer Protocol (SMTP) for email, and File Transfer Protocol (FTP).
Historical development
The suite's origins are deeply tied to the ARPANET, a pioneering network funded by the United States Department of Defense. In the early 1970s, researchers including Vint Cerf and Bob Kahn began developing a protocol to interconnect disparate packet networks, an effort later managed by DARPA. A pivotal demonstration occurred in 1977, linking the ARPANET, the Packet Radio Network, and the Satellite Network. The protocols were formally adopted as the standard for the ARPANET on January 1, 1983, known as the "flag day." Their proliferation was accelerated by their integration into the Berkeley Software Distribution (BSD) variant of Unix, and later cemented by the commercialization of the Internet and the creation of the World Wide Web by Tim Berners-Lee.
Applications and services
Virtually every modern networked application relies on the TCP/IP suite. The World Wide Web, invented at CERN, operates over HTTP. Email services use protocols like SMTP, Post Office Protocol (POP), and Internet Message Access Protocol (IMAP). File sharing utilizes FTP or peer-to-peer protocols. The Domain Name System (DNS), a critical distributed directory service, translates human-readable names like "www.example.com" into IP addresses. Real-time communication, such as video conferencing on platforms like Zoom, often uses Real-time Transport Protocol (RTP) over UDP. Cloud computing infrastructures from Amazon Web Services and Google Cloud Platform are built upon this foundational protocol stack.
Security considerations
The original TCP/IP design prioritized functionality and resilience over security, leading to inherent vulnerabilities. Issues like IP spoofing, man-in-the-middle attacks, and packet sniffing are possible because core protocols lack built-in authentication and encryption. In response, additional security protocols have been developed and deployed. Secure Sockets Layer (SSL) and its successor, Transport Layer Security (TLS), now secure web traffic (HTTPS). The Internet Protocol Security (IPsec) suite provides security at the network layer for virtual private networks (VPNs). Ongoing efforts by the IETF and security researchers address threats from large-scale distributed denial-of-service (DDoS) attacks, often orchestrated via botnets like Mirai.
Category:Internet protocols Category:Computer networking